Recommendations
The recommendations dashboard offers insights into the different aspects of cloud governance categories and provides a list of impacted resources and resolution options.
While the findings mentioned in every dashboard have individual recommendation view buttons, in the Recommendations dashboard, these are grouped under a policy name.
This dashboard is split into two main sections – Summary and All Recommendations.
Summary
This section shows 5 types of crucial data:
- Total Recommendations – This shows the total number of recommendations
- Open Recommendations – This shows the number of unresolved and open recommendations
- Skipped Recommendations – These are the recommendations that have been acknowledged but will not be resolved. The user wants the status quo maintained
- Resolved Recommendations – This shows the number of resolved and closed recommendations
All Recommendations
As a FinOps practitioner, you can see cost recommendation for following data points, so that you can cross-validate the recommendation and be absolutely sure that applying the recommendation will not affect the system performance, availability and so on.
- Source of the recommendation
- Recommendation generated date
- Rules applied for generating the recommendation
the source of the recommendation and the rules used to generate the recommendation when generated by CoreStack so that i can cross-validate the recommendation and be absolutely sure that that applying the recommendation will not affect my system performance, availability etc.
As a finops practitioner, i would like to understand the age of the recommendation of that i can be sure that the recommendation is still valid for applying on a resource
Toggle View
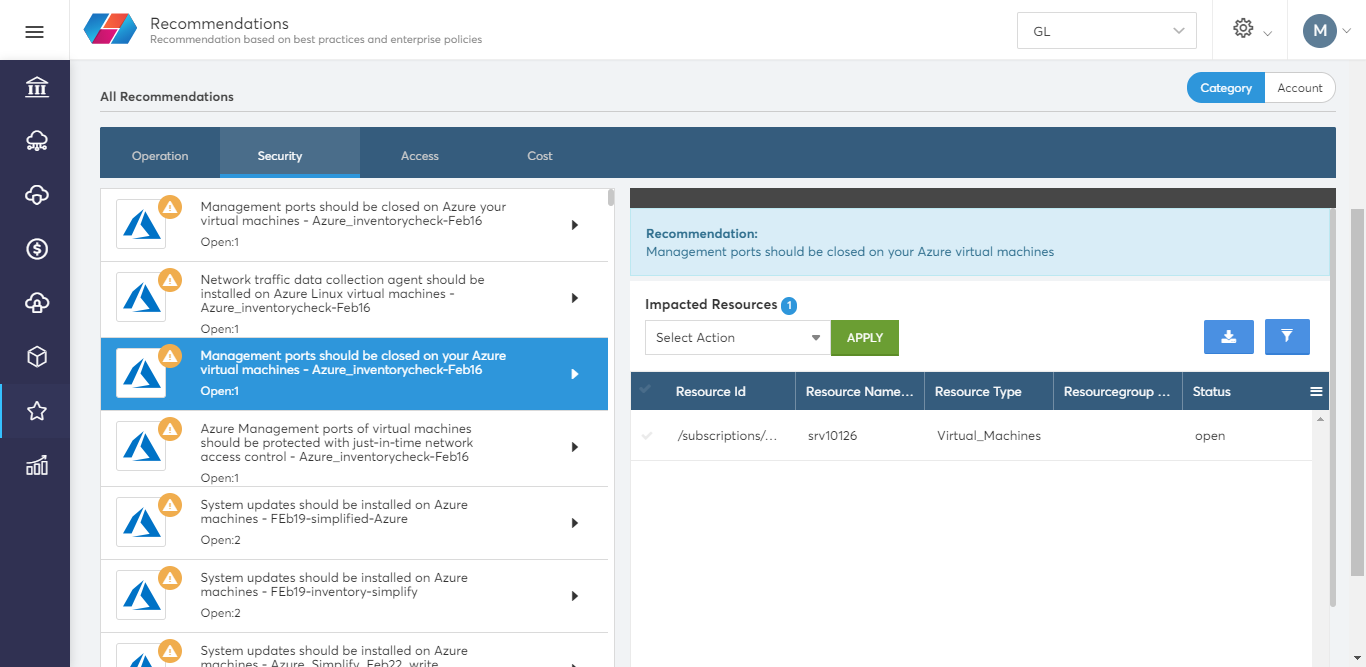
You can toggle the view to list the recommendations as per Category or Account. Let's click category to view the recommendations filtered for Operations, Security, Access and Cost Optimization categories.
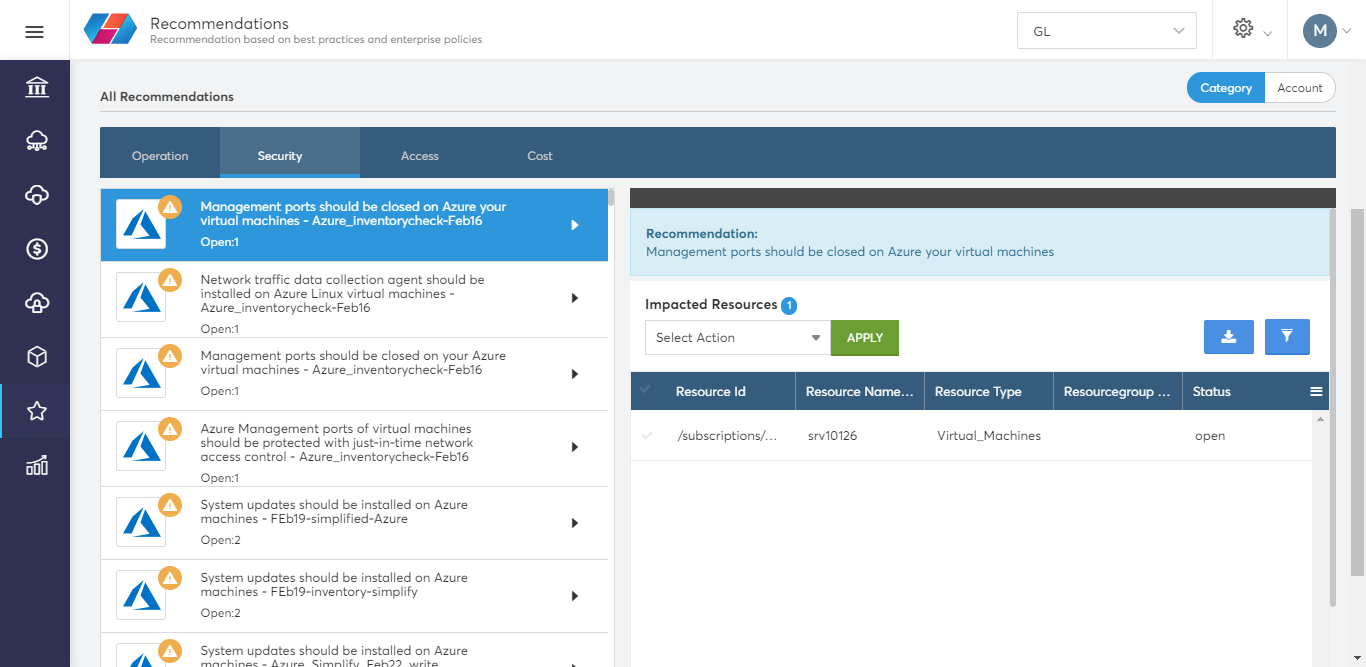
Click on a recommendation to view it in detail and obtain the list of impacted resources.
Resolving Violations using Recommendations
The proposed action for every recommendation varies based on the resource type and the nature of violation. For example, for a storage policy, it can be delete storage, for a security group policy it can be revoke rule, etc.
Action Taken – This proposed action will resolve the issue by correcting the fault. For example, if an RDP port is open, using the proposed action "revoke" will close the port. Also, it will ensure that from the next time the system itself will close the port and not allow it to become a security finding.
Skip – This action will acknowledge the issue but will not have any impact on the finding. CoreStack's machine learning capabilities will learn to not mark it as a security finding in the future.
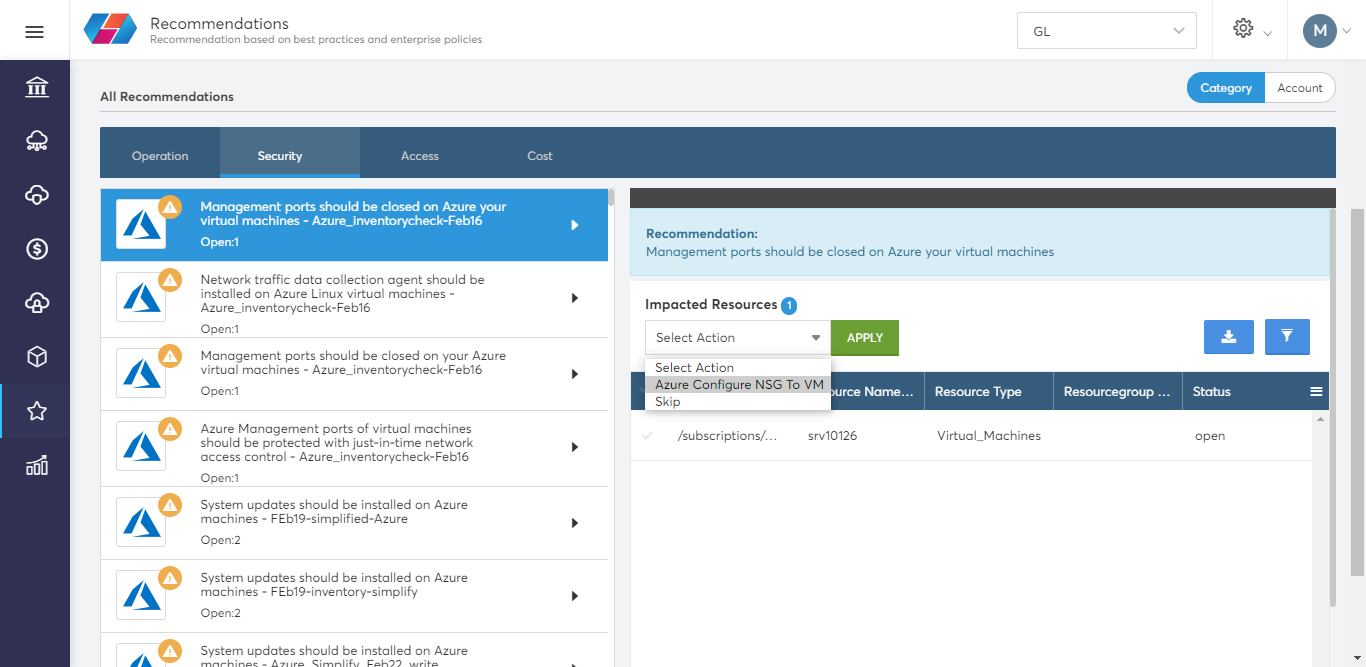
Steps to apply actions to a recommendation:
- Click on a recommendation to view the list of impacted resources.
- In the Impacted Resources list, select a resource and then from the drop-down menu select an action.
In this example, we select a Security Group policy related recommendation, and revoke the SecurityGroup rule.
The rule has been revoked and the recommendation has helped resolve the security finding.
Updated 7 months ago